Massive SQL injection attacks hit thousands
12 June 2008
Microsoft SQL Server has always been open to easy exploits, and
according to this
new report, overseas attackers managed to infiltrate more than
half a million websites, including those of the United Nations and
the US Department of Homeland Security.
Along with the major flop
of Microsoft Vista operating system, this news is another reminder
of the inferior quality of Microsoft data management software.
Wired magazine notes that, by itself, Microsoft is not secure:
"While the attack is
not Microsoft's fault, it is unique to the company's IIS server.
The automated attack takes advantage to the fact that
Microsoft’s IIS servers allow generic commands that don’t
require specific table-level arguments. However, the
vulnerability is the result of poor data handling by the sites’
creators, rather than a specific Microsoft flaw.
In other words, there’s no patch that’s going to fix the issue,
the problem is with the developers who failed follow
well-established security practices for handling database input.
The attack itself injects some malicious JavaScript code into
every text field in your database"
PC World Magazines notes that over 10,000 web sites running
Microsoft have been attacked from an IP address in China:
"The attackers aren't targeting a
specific vulnerability. Instead they are
using an automated SQL injection attack
engine that is tailored to attack Web
sites using SQL Server, Huang said. The
attack uses SQL injection to infect
targeted Web sites with malware, which
in turn exploits vulnerabilities in the
browsers of those who visit the Web
sites, he said, calling the attack "very
well designed."
The caveat is clear. Neither Oracle nor SQL
Server are secure out-of-the-box.
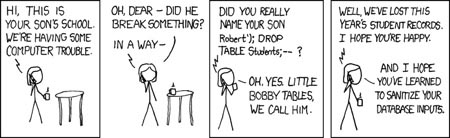
Inside SQL Injection attacks
This scary
must-see video that shows a real-world SQL injection attack and
it's frightening how fast they can break into a allegedly secure
database. It's even more frightening that someone would publish
step-by-step instructions where the criminals can see them.
This video
shows a SQL Injection attack in Linux, "based on a true story",
giving criminals complete directions to aid them in their acts.
See my related notes on Oracle SQL injection attacks:
|
