 |
|
Evaluating the honesty of the IT professional
Job Interview Tips by Burleson Consulting
Septembers 29, 2007
|
This is an excerpt from the
upcoming book "Win
your Computer Dream Job", by Rampant Techpress.
Honesty is the best policy
More than ever before, computer
systems are being compromised by dishonest and unstable IT professionals,
and the news is full of reports about employee theft and abuse.
Whether it's simply altering data for personal gain or selling
mission-critical information to your business competitors,
management is challenged to screen-out anyone with a history or
predisposition for dishonesty. In some cases, it's
considered malfeasance to fail to carefully check-out anyone who
has access to your confidential data.
See these important notes on
how to
use bad credit reports against employees and
a
sample questionnaire to screen employees for immoral histories.
The influx of dishonesty in the IT
profession is due to several factors:
-
Expanding demand - As the need for
computer professionals outstripped supply, desperate companies were forced
to lower their hiring standards. For example, companies who used to
required newbies to be graduates from AACSB accredited universities were now
forced to entertain applicants from community colleges.
-
No barriers to entry - Unlike other
professions that require licensing and certification (e.g. Engineers,
Accountants, Architects), anyone can hang out a shingle proclaiming
themselves to be a computer expert.
Given these market conditions,
fly-by-night computer "colleges" sprang-up everywhere,
enticing marginal blue-collar workers with the promise of a
well-paid professional lifestyle. Offshore diploma mills
sprang-up on the web, offering instant degrees, complete with a
telephone answering service disguised as a Registrars office,
all of this with the intent to deceive HR departments when
verifying a college degree.

The lucrative lifestyle of an IT profession attracts thousands of
marginal people
IT managers have noted a sharp
increase of acts of moral turpitude in the computer industry
over the past decade and
they are going to great expense to ensure that their new
computer professionals will not pose a risk to their mission-critical data.
The stakes are high, and the new is full of reports of companies
that have lost millions of dollars due to the
immoral
behavior to employees.
-
In Florida,
William Sullivan faces accusations that he stole millions of records
from the database, selling his employers mission-critical data to a data
broker.
-
In California,
Jennifer Adams, 45, an IT systems administrator, allegedly orchestrated
a tax fraud scheme that scammed the government out of more than $50,000.
These insider threats are a major concern
throughout the IT industry and CIO's everywhere are investing in tools to
identify dishonest computer professionals.
|

"Robert Allen", Fake expert |
Within the world of Oracle
database management we also see dishonesty, with unworthy scholars from around
the globe labeling themselves as "Oracle Experts".
While many just lie
about their credentials and work history, some dishonest characters like Ed
Haskins
created Oracle expert "Robert Allen" for his Phishing web site.
Read
here from eWeek how Burleson Consulting helped to uncover
this dishonest computer professional.
|
In light of the rampant dishonesty within the
computer profession, IT management has a responsibility to
carefully screen computer employees, especially those in trusted positions
such as IT management, the Database Administrators and Systems Administrators,
and it's now "due diligence" to investigate all job candidates to ensure that
they don't hire anyone with a propensity to be dishonest. For example, within Burleson Consulting,
our clients expect us to
perform extensive
pre-employment screening, evaluating every aspect of a job applicants public
records, work history and personality:
"In lieu of an active US security clearance,
candidates must pass a background check and be free of any criminal
convictions (except minor traffic violations).
Further, any acts of moral
turpitude (history of drug use, dishonesty, lying, cheating, theft) are
grounds for immediate rejection, and all applicants must sign a waiver to
disclose personal information and agree to submit to a polygraph exam."
Let's take a closer look at how your personal and work history are evaluated for
evidence of dishonesty.
Evaluating the personal integrity
of a IT job applicant
Corporations make a sharp distinction between
"cash register honesty" and trustworthiness, and millions of dollars are devoted
each year to evaluate the honesty of computer employees. Many of their
techniques are not new and draw from proven success stories:
-
Elliott Ness ? During the corruption of
the 1930?s Chicago gangs, Ness carefully evaluated the backgrounds of law
enforcement to chose incorruptible personnel for his legendary squad ?The
Untouchables?.
-
Howard Hughes - The eccentric
millionaire performed extensive background checks to find a team of
trustworthy employees.
-
Uncle Sam - The government has an
excellent record of evaluating personal integrity for sensitive government
jobs. See here for details on the
requirements for US security
clearance.
One benefit of today's connected
world is the ability to glean personal information from many
public records. Background check services offer public
details that can shed light on the personal integrity of a
computer job applicant:
- Court Records
- While companies have always checked for criminal
histories, many are now pursuing other public records for
evidence of moral turpitude. These include divorce cases
and civil litigation.
- Credit history
- Companies routinely perform credit checks
seeking evidence of dishonesty and disregard for obligations such as late
payment history.
- Google - Almost all companies invest in services that check-out a
job applicant on the web, and it's amazing how much personal information
people will disclose in chat rooms for forums.
- Unobtrusive measures - Companies routinely do a surprise
pre-employment drug test and require job candidates to agree to written
testing, all in the quest for evidence of dishonesty. Some companies
arrange a golf interview because golf is a fantastic way to access the true
personality of an IT job candidate.
Remember, companies are very careful not to disclose the reason for rejecting
a job candidate, and legally they don't need any reason. Within states with "at will" hiring statutes, computer shops are free to
reject job candidates for the slightest hint of impropriety.
Objective measures of dishonesty
Many IT shops use the same
hiring criteria as outlined in US Federal Regulations,
PART 710?CRITERIA AND PROCEDURES FOR DETERMINING ELIGIBILITY FOR ACCESS TO
CLASSIFIED MATTER. Any of the following
are evidence or moral turpitude, someone that cannot be trusted with sensitive
corporate data:
- arrest
and/or conviction of a felony;
-
frequent involvement with authorities even as a juvenile;
- DWI/DUI;
- having
been a patient in an institution primarily devoted to the treatment of
mental, emotional, or psychological disorders;
- A
history of not meeting financial obligations. A pattern of financial
irresponsibility (bankruptcy, debt or credit problems, defaulting on a
student loan);
- moving
violations with fines over $200;
-
illegal drug use (to include any use of cocaine,
heroin, LSD, and PCP); and the illegal purchase, possession, or sale of any
such narcotics.
-
Deceptive or illegal financial practices, such as embezzlement, employee
theft, check fraud, income tax evasion, expense account fraud, filing
deceptive loan statements, and other intentional breaches of trust
-
Inability or unwillingness to satisfy debts
-
Unexplained affluence
-
Financial problems that are linked to gambling, drug abuse, alcoholism, or
other issues of a security concern.
-
Deliberate omission, concealment, or falsification of a material fact in any
written document or oral statement in the job application
But today's IT managers must go beyond public
records to evaluate personal honesty, and many shops use a Psychologist to help
evaluate job candidates for sensitive computer jobs.
Some companies develop a personality profile for job candidates,
rating potential computer employees for these factors:
-
Vulnerability - Omissions in the job
application and willful concealment of embarrassing personal incidents (e.g.
acts of sexual deviance), can make a computer employee vulnerable for
engaging in illegal behaviors.
-
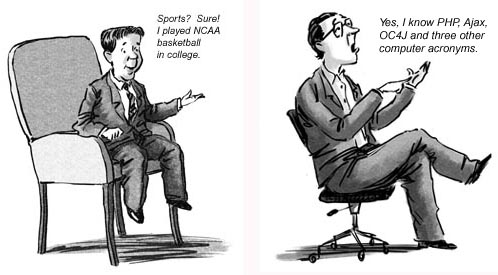
Exaggeration - IT job candidates who
"puff" their job responsibilities, education or work history are quickly
disqualified as dishonest.
-
Poor Judgment - Potential employees are
evaluated (by speaking to ex co-workers where the laws of job privacy do not
apply), seeking to find any evidence of contempt for management, anger
issues, stalking behaviors, excessive absences from work and lying to
cover-up mistakes.
-
Scofflaws - Companies routinely check a
job applicants background seeking unobtrusive measures to find a "scofflaw",
seeking evidence of subtle dishonesty. This can include a history of
drunk driving, shoplifting, multiple traffic tickets and possession of
drugs.
-
Sue-ers - A history of civil litigation
relating to personal matters (unpaid child support, allegations of bad
parenting) is a red flag, as-is a history of frivolous actions in small
claims court.
Getting to know you . . . getting to know
all about you
There are many employment screen
services that will scour the web, searching for evidence of
dishonesty. In trained hands, Google can discover volumes
about a job applicant. I remember a case where a
job applicant was rejected for something that they did back in
1998 (it was an unprofessional remark in a USENET Newsgroup).
In another memorable case, a job candidates was rejected because
his Facebook page contained a photo of him holding a "bong" (a marijuana
delivery vehicle).

Your facebook photos can be used against
you
Unfortunately, web searches can also be abused and there are no
government regulations about using information about you that
has been gleaned from the Internet. . This Stanford University research paper titled
"Managing Risk
to Reputation" (2005 STAN. TECH. L. REV. 2), we see a recognition
that Google is indeed being widely used as a reputation
screening tool:
with the increased role that Internet message boards play the
recruitment process, law firms have found that their reputation with law
students has become more volatile.
Of course, employers have a responsibility to verify all
information about you that is gleamed from the web, especially
since cases of
"Cybersmearing" are increasing:
Some corporate victims have filed lawsuits seeking to
identify the posters of the cybersmear and hold them accountable for their
actions, and the numbers of companies willing to sue to protect their good
name and reputation is growing fast.
Unfortunately, you will never know if you have been rejected
because of something that you wrote (or was written about you),
so companies like "Reputation
Defender" can be used to remove false and malicious
information about you..
Let's take a closer look at some other mechanisms that are used to verify the
honesty of the computer job applicant.
Testing for personal integrity
An on-site computer job interview for IT managers may also
contain other unobtrusive methods for evaluating honesty.
My golf instructor, (PGA Master Professional Brad Clayton) is
engaged by large corporations to arrange a test of personal
integrity, cleverly disguised as a golf outing. This
seemingly innocuous act of golfing reveals volumes about a
job candidates personal integrity and temperament, and many of
the golfing job interviews are "rigged", providing the job
candidate with an opportunity to cheat without being seen.
But golfing is just one way to get under the covers and see the
job candidates true honesty.
Many IT shops are using psychological testing, using proven
personality test like the Minnesota Multiphasic personality
Inventory (MMPI) to identify people with a borderline
personality disorder that might compromise their honesty on the
job. See our related notes on
personality profiling for Business Success.
Most important is the MMPI "lie" scale, which measures whether
the job candidate is is trying to manipulate their test
results. In the world of
Information Technology, job candidates are evaluated for several
traits:
-
Unwarranted fears - Psychologists have noted that job candidates with
phobias and a high fear of rejection correlate with low self-esteem and
anger issues, both of which can influence personal honesty.
-
Unstable self image - Someone with a history of short employment
tenure is a major red flag and sudden changes in career goals is a very bad
sign.
-
Impulsive traits - Impulsivity is sometimes a sign of an employee
with low morals, and is evidenced with a history of gambling, irresponsible
spending and reckless driving.
The
MMPI test is a set of 500 true/false questions that accesses personality
with remarkable validity, and it's results are accepted in all U.S. courts.
Their test-base consists of hundreds of thousands of subjects,. with a
pre-diagnosed mental disorder (see
DSM IV). By
comparing their responses to seemingly innocuous questions (e.g. "I read the
editorials in the newspaper every day") a proven predictive model was created (Federal
courts have affirmed the MMPI as a scientifically valid) and accepted
procedure for personality assessment.
For example, the subjects preference to take showers vs.
baths is an extremely reliable measure of self-esteem, and other scales such as
the "Mach" scale that measures how manipulative you are (based on the
bestselling book "The Prince" by Machiavelli. Here is an excellent
overview of the MMPI
scales and how they access your personality with eerie accuracy.
These MMPI scales are all valuable for ?getting inside?
someone?s personality, and the results are often used as evidence in criminal
and civil (especially child custody) cases.
Honesty is the best policy
When being evaluated, a candidates honesty is valued far more than
sub-optimal work performance. For example, consider this case where a
group of Federal agents were doing a stakeout when one of the agents
accidentally discharged their firearm. The fellow agents agreed to
"ignore" this incident in a misplaced attempt to keep their co-worker from being
reprimanded. When the mistake was brought to light, the agent who made the
mistake freely admitted the indiscretion, while his co-workers were fired for
covering-up the indiscretion.
Never lie or "puff" during a job
interview
While the polygraph results are not admissible in court,
there is no denying that people do have a physiological response to deception.
The use of polygraphs as a hiring tool is permitted for certain computer
occupations as outlined by The Employee Polygraph Protection Act (EPPA).
EPPA allows a pre-employment lie detector test for anyone applying for a
computer job with the US government, any employers who distribute controlled
substances (narcotics).
If you aspire to a high-level job in IT, be prepared to
have every aspect of your life examined, and always admit any immoral of
embarrassing details, even if you don't think that there is any verifiable
evidence. You can safely assume that your background will be thoroughly
examined and you may even be asked to submit to a polygraph (lie detector) test.
Remember, honesty is the ONLY policy when applying for a
computer job. You are far more likely to be dismissed for concealment than
for the acts themselves.
